

King size candy bars, give out 2 to each. Everyone always loved that guy


King size candy bars, give out 2 to each. Everyone always loved that guy


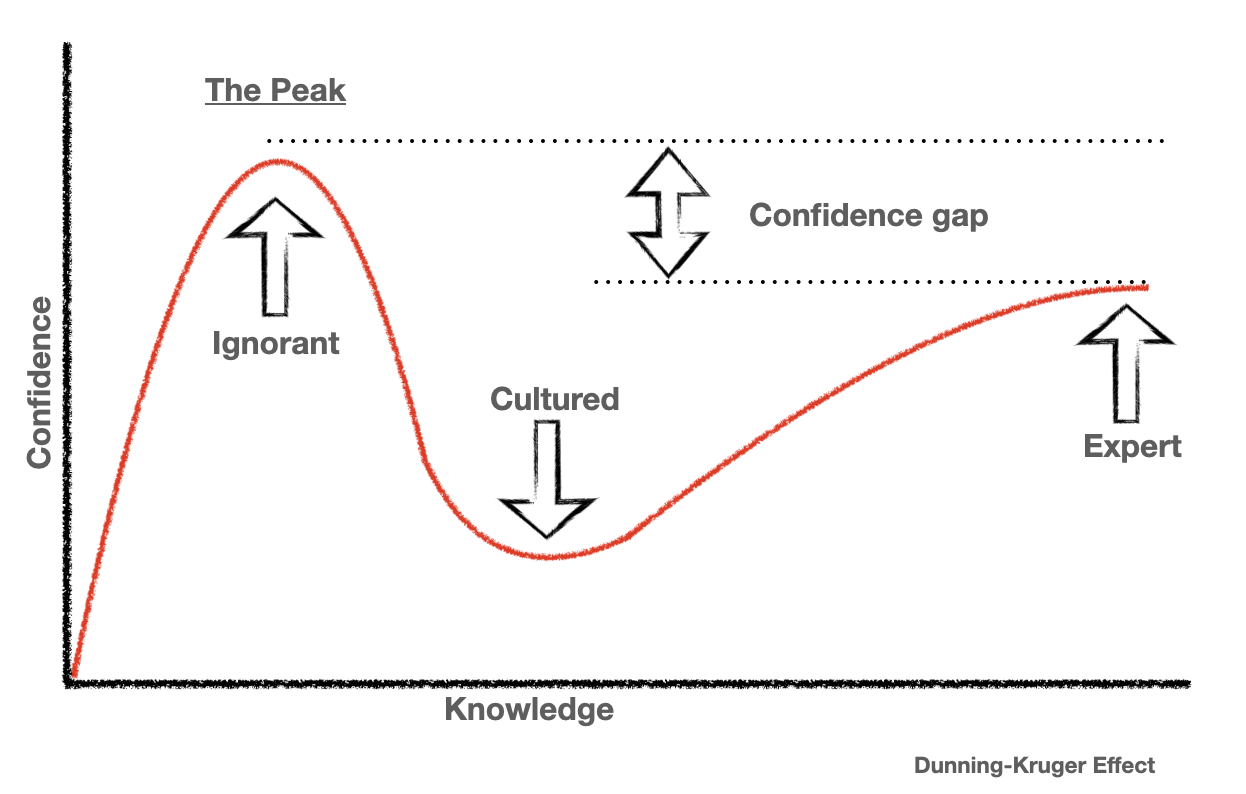
The thing about rational actors, is when given the same information they should make the same choices. I would argue that they’re most likely, instead, just at the peak of mt. stupid


We shouldn’t blame the victims that society failed to properly educate. You’re right that if people intimately understood apple the way you probably do, they’d never buy an apple product. I would argue, however, that it’s a failing of education not an informed choice to be corporately cucked.


I don’t think anyone should expect a battery replacement to be free after 10 years, but it shouldn’t cost $100,000
Just because you can’t use it doesn’t mean a hacker can’t. If someone discovered a vulnerability in the 3g handshake or encryption protocol, it could be an avenue for an RCE.
I run ubuntu’s server base headless install with a self-curated minimal set of gui packages on top of that (X11, awesome, pulse, thunar) but there’s no reason you couldn’t install kde with wayland. Building the system yourself gets you really far in the anti-bloatware dept, and the breadth of wiki/google/gpt based around Debian/Ubuntu means you can figure just about any issues out. I do this on a ~$200 eBay random old Dell + a 3050 6gb (slot power only).
For lighter gaming I’ll use the Ubuntu PC directly, but for anything heavier I have a win11 PC in the basement that has no other task than to pipe steam over sunshine/moonlight
It is the best of both worlds.


the best way to learn is by doing!


I just built my own automation around their official documentation; it’s fantastic.
https://www.wireguard.com/#conceptual-overview


vyatta and vyatta-based (edgerouter, etc) I would say are good enough for the average consumer. If we’re deep enough in the weeds to be arguing the pros and cons of wireguard raw vs talescale; I think we’re certainly passed accepting a budget consumer router as acceptably meeting these and other needs.
Also you don’t need port forwarding and ddns for internal routing. My phone and laptop both have automation in place for switching wireguard profiles based on network SSID. At home, all traffic is routed locally; outside of my network everything goes through ddns/port forwarding.
If you’re really paranoid about it, you could always skip the port-forward route, and set up a wireguard-based mesh yourself using an external vps as a relay. That way you don’t have to open anything directly, and internal traffic still routes when you don’t have an internet connection at home. It’s basically what talescale is, except in this case you control the keys and have better insight into who is using them, and you reverse the authentication paradigm from external to internal.


Talescale proper gives you an external dependency (and a lot of security risk), but the underlying technology (wireguard) does not have the same limitation. You should just deploy wireguard yourself; it’s not as scary as it sounds.


Fail2ban and containers can be tricky, because under the hood, you’ll often have container policies automatically inserting themselves above host policies in iptables. The docker documentation has a good write-up on how to solve it for their implementation
https://docs.docker.com/engine/network/packet-filtering-firewalls/
For your usecase specifically: If you’re using VMs only, you could run it within any VM that is exposing traffic, but for containers you’ll have to run fail2ban on the host itself. I’m not sure how LXC handles this, but I assume it’s probably similar to docker.
The simplest solution would be to just put something between your hypervisor and the Internet physically (a raspberry-pi-based firewall, etc)


Devil’s Advocate:
How do we know that our brains don’t work the same way?
Why would it matter that we learn differently than a program learns?
Suppose someone has a photographic memory, should it be illegal for them to consume copyrighted works?
It’s fuckin’ art though


Oracle, SAP, Redhat, all of their customer portals require it for SSO. I’m not saying it should be that way, but it is.


I think you go about it the other way: break data analytics and advertising off from everything else. If every unit has to be self-sufficient without reliance on data collection and first-party advertising I think you fix most of the major issues.


I’m actually working on a vector DB RAG system for my own documentation. Even in its rudimentary stages, it’s been very helpful for finding functions in my own code that I don’t remember exactly what project I implemented it in, but have a vague idea what it did.
E.g
Have I ever written a bash function that orders non-symver GitHub branches?
Yes! In your ‘webwork automation’ project, starting on line 234, you wrote a function that sorts Git branches based on WebWork’s versioning conventions.


+1 for cmk. Been using it at work for an entire data center + thousands of endpoints and I also use it for my 3 server homelab. It scales beautifully at any size.
Are you maybe thinking of https://distr1.org/ made by the i3 guy?
Yes and no. In the best case, endpoints have enough cached data to get us through that process. In the worst case, that’s still a considerably smaller footprint to fix by hand before the rest of the infrastructure can fix itself.
This is probably the play they’re making; the only thing that makes me think it might be something else is that they also announced ditching proprietary code in favor of kvm in workstation. Makes me wonder if they instead are deciding to slowly kill the product line, and instead of just stopping development entirely, they’re giving it out as if it’s some huge gift to try and “buy” good will before it becomes an inferior product?
Either way, support costs for the product are now $0 (because you can’t buy it) and development costs are about to be near-zero if they’re forking upstream kvm.
https://www.phoronix.com/news/VMware-Workstation-KVM